Posts by Lance
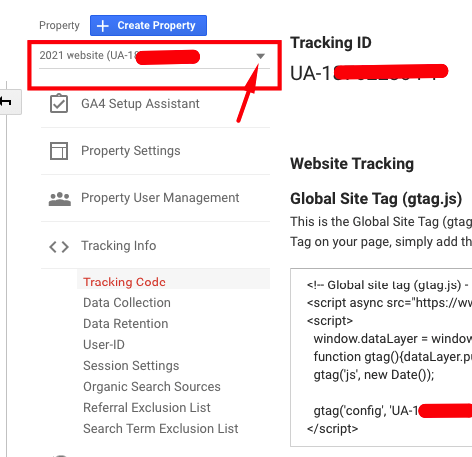
How to generate Google Analytics UA code in new GA4 platform
When Google Analytics upgraded in October 2020 the ability to create a UA- ID for website tracking became a bit hidden (by a lot). Luckily there is a simple series of steps to support websites that only accept UA- code tracking over use of the new gtag.js method. From your Google Analytics ‘Admin’ goto the…
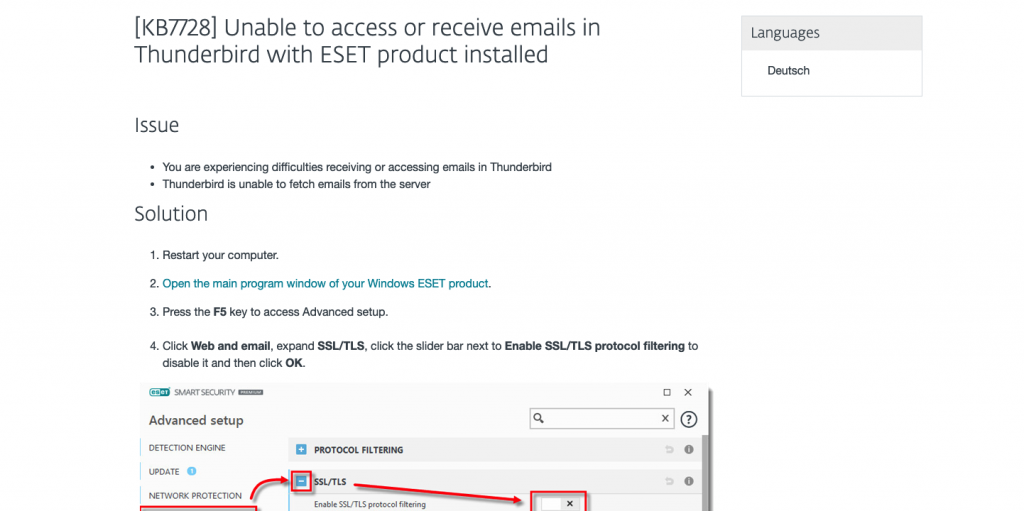
Read MoreThunderbird mail not working after 1 December?
If you’re using Eset security on your PC and Thunderbird for an email client they will have stopped working on 1 December. The simple workaround was to disable Eset (webmail and email filtering). There is a permanent solution and it’s pretty simple. It was all to do with Eset replacing their security certificate. Thunderbird didn’t…
Read MoreHave you done enough to be compliant for the Privacy Act 2020?
If you’re in business the Privacy Act 2020 affects you Shortly the 2020 version of the Privacy Act comes into effect (1 December). Its purpose is to catch-up a lot of the ground between its initial 1993 deployment and the current way of the world and bring New Zealand closer to the European standard General…
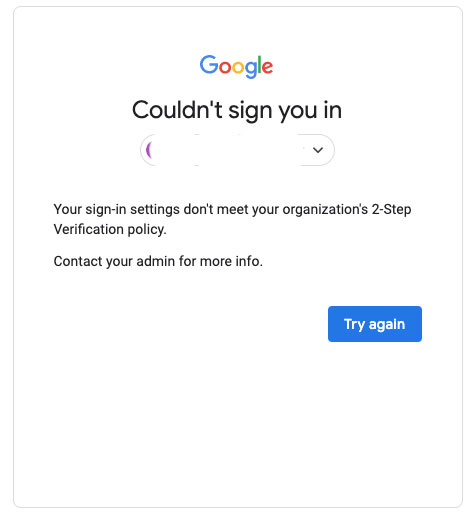
Read MoreError when logging into Google account: Your sign-in settings don’t meet your organization’s 2-Step Verification policy
Updating to Google’s login security is preventing authorised access for some users. Try again won’t work either. It is easy to resolve. First you need to log into the master Google account via admin.google.com – the Admin console. Log into the account you’re trying to access. It will now ask you to enter one of…
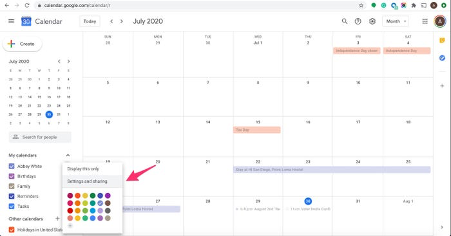
Read MoreMicrosoft Outlook natively supports Google calendar on Mac not on PC
If you use Google Mail and its associated calendar, they work a treat using Outlook on macOS to share your calendar across devices however if you’re a PC user there are a few extra steps. ** Update: I’ve been using a freeware app in a couple instances that sorts this right out. More details at…
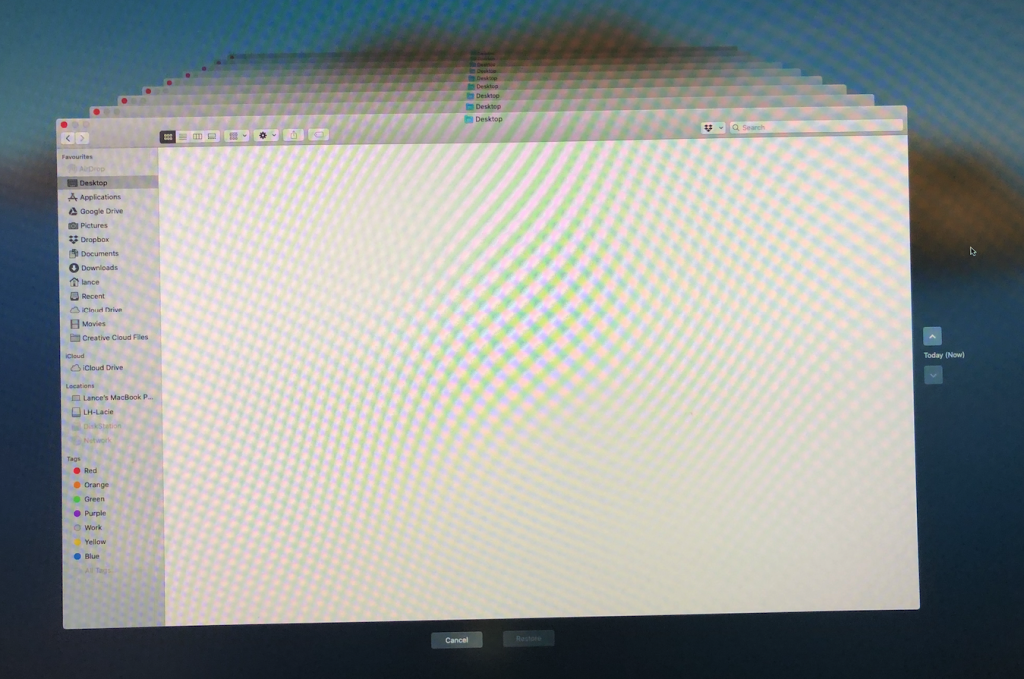
Read MoreDon’t use Time Machine with your NAS/Network storage
What seems like a great idea will deliver great heartache when you need that Time Machine backup and the only or most up-to-date copy is in a network storage location. The heartache will start when you can’t access that network drive location, when you’re doing a system restore following a catastrophic failure. You’ve suddenly got…
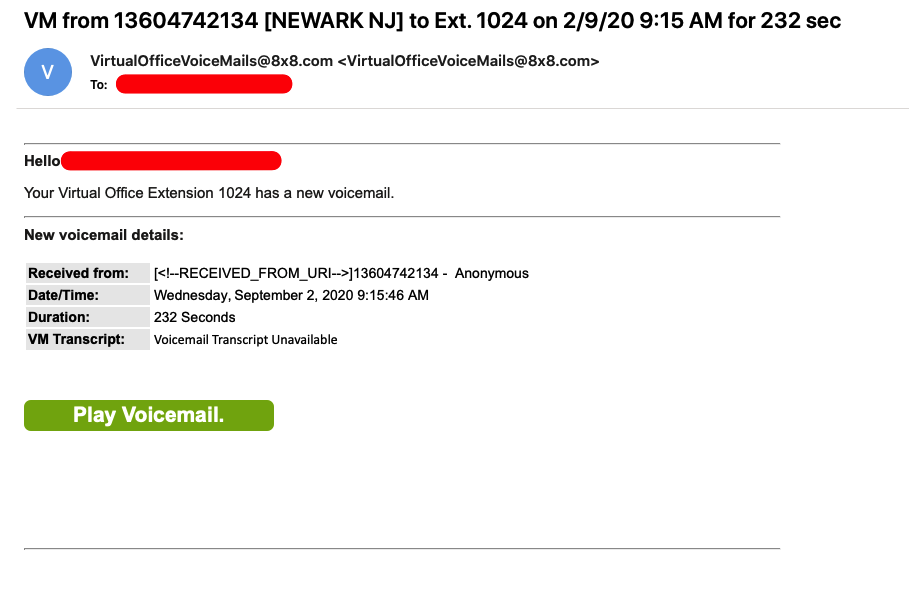
Read MoreWatch out for voicemail emails
Today a new email notification of a voicemail arrived – that proved to be illegitimate. Like all phishing instances, this was very cleverly done, right down to the sending of the email to spoof as being legitimate. Making it even more convincing, the URL contained in the email tied it to the sending platform –…
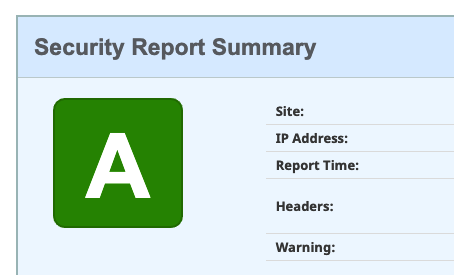
Read MoreSecuring your website with https:// is not enough
Unless you’ve recently had your website security upgraded, chances are it is vulnerable. For most websites there is a momentary window of opportunity for hackers to bust it open if they test its ability to redirect from the http:// to https:// address. It is a cat-and-mouse game of shoring up against hackers, for them to…
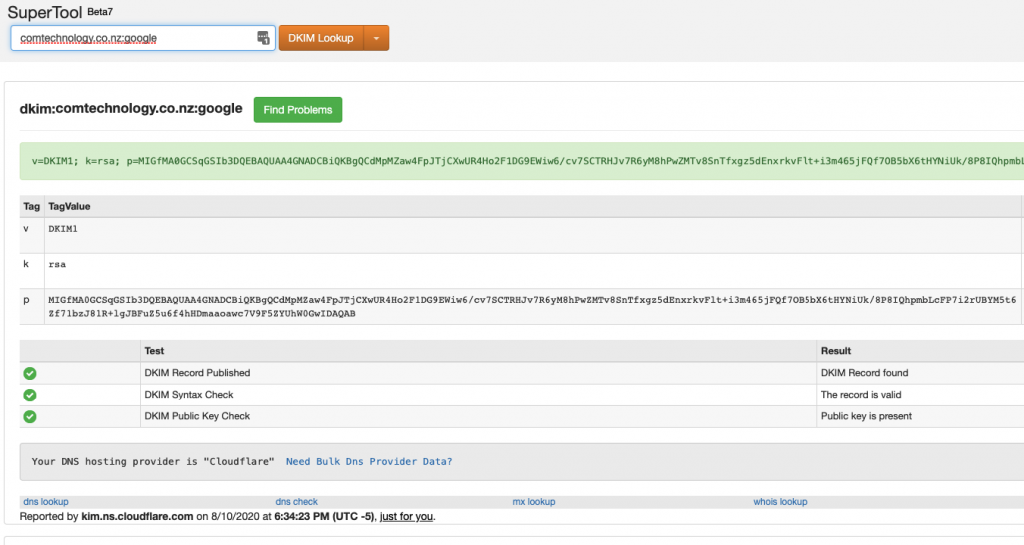
Read MoreIs your email account scam resistant?
Knowing how reliant your business is on email requires you be one step ahead of the scammers. That starts with using a premium level service provider and, if you’re using a mail service attached to your domain name, that it is configured to deflect spam and scams. What used to be ‘okay’ in terms of…
Read MoreDo not click the link in the email!
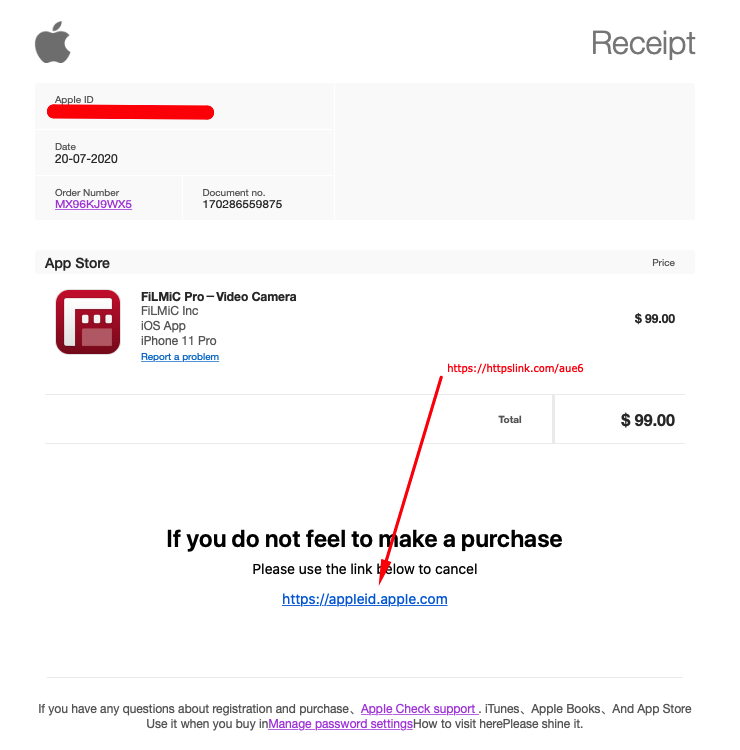
Did you get an email from Apple about purchasing something from their App store? Take a good look at it and have a good think. Most of all, don’t click the link! That it appeared in my junk box was the first clue that was where it was meant to be. It looks like the…
Read More